CISA KEV Vulnerabilities
The CISA KEV Vulnerabilities charts identify vulnerabilities in your environment that appear in CISA’s Known Exploited Vulnerabilities (KEV) catalog — an authoritative list of vulnerabilities confirmed to be actively exploited in the wild. Maintained by CISA, the KEV catalog is a key resource for helping prioritize remediation based on real-world threat activity.
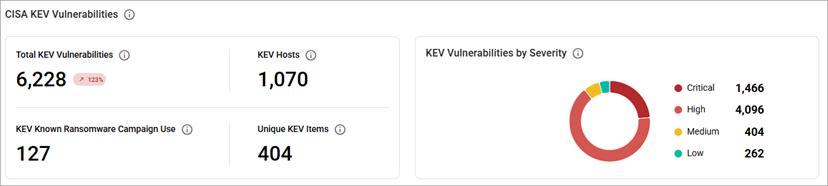
The CISA KEV Vulnerabilities charts include:
- Total KEV Vulnerabilities chart—shows the total count of vulnerabilities in your environment that are related to entries in CISA’s Known Exploited Vulnerabilities (KEV) catalog, along with a trend from the previous scan. These are confirmed, actively exploited vulnerabilities and should be prioritized for remediation.
- Note: If you select the number in the Total KEV Vulnerabilities chart, you will be redirected to the CISA KEV Vulnerabilities tab with all KEV vulnerabilities.
- KEV Hosts chart—shows the number of hosts in your environment affected by one or more vulnerabilities listed in CISA’s Known Exploited Vulnerabilities (KEV) catalog. These systems are at higher risk and should be prioritized for investigation and remediation.
- Note: If you select the number in the Kev Hosts chart, you will be redirected to the Hosts Tab filtered to show only hosts with KEV vulnerabilities.
- KEV Known Ransomware Campaign Use chart—shows the number of distinct vulnerabilities from CISA’s Known Exploited Vulnerabilities (KEV) catalog that have been identified across your environment and are known to be associated with ransomware activity.
- Note: If you select the number in the KEV Known Ransomware Campaign Use chart, you will be redirected to the CISA KEV Vulnerabilities tab with Ransomware Campaign Use filtering set to Known.
- Unique KEV Items chart—shows the number of distinct vulnerabilities from CISA’s Known Exploited Vulnerabilities (KEV) catalog that have been identified across your environment.
- Note: If you select the number in the Unique KEV Items chart, you will be redirected to the CISA KEV Vulnerabilities tab with default filtering.
- KEV Vulnerabilities by Severity chart—shows a breakdown of all CISA KEV-related vulnerabilities in your environment by severity.
- Note: If you select the number in the KEV Vulnerabilities by Severity chart, you will be redirected to the CISA KEV Vulnerabilities tab with default filtering.
Related Topics